This is not primarily about the security of attaching to a wireless access point (WAP). But since communication is a two way affair, let’s start with the endpoints and get them out of the way:
You are more likely to have your purse snatched at a train station than in your living room. And the chances of it happening inside a café seem like it is between the two. Even though the café is a public place, the purse snatcher needs to get out the door to escape and that can be tricky so there is some deterrent to them operating in a café.
Public access WiFi is not much different than that. A rogue WAP is most likely looking for you in the most public places, least likely looking for you in your living room where the WAP you attach to is most likely one you own and if you stick to the SSID that the café says is safe, you are mostly ok there. (Security professional’s mandatory warning: be safe- change the default password on the admin account on your wireless access point in your house. Now.)
Now, let’s talk about how we treat our guests. If you’re like many people, you are always looking to hop onto the guest WiFi where you are. The rest of this post looks at the guest WiFi from the WAP provider’s perspective. What does real courtesy involve? In other words, how should we treat our guests?
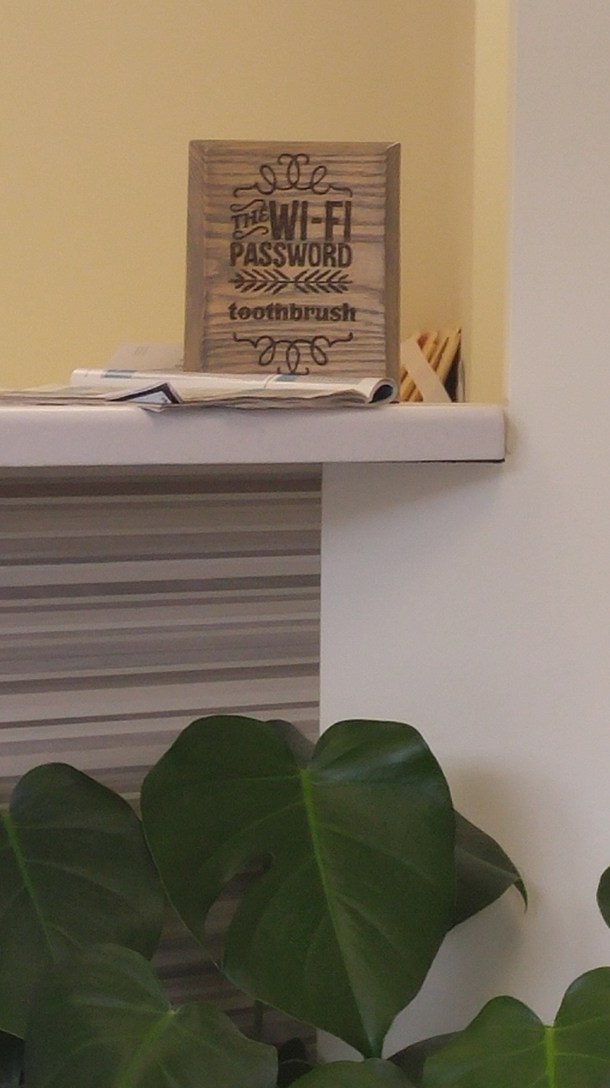
- Have a password but not an elaborate procedure. It is best to be running guest on an encrypted channel so someone can’t eavesdrop on your guests. This is easiest if you give the guests a password. But keep in mind: the password is to establish an encrypted session, not to keep people off the guest WiFi. It’s a component of a network protocol not an access control. So an elaborate, changes all the time, takes three steps, we’ll text you an access code, etc. procedure is no way to treat a guest. Don’t build in useless access control measures if you are really open to providing WiFi to all comers.
- Determine if you really mean “guest WiFi.” Maybe you mean “still controlled but not my intranet.” That’s ok. But then don’t call it guest WiFi, call it “invitation only” WiFi. Nothing wrong with that. Maybe you have a privileged group of visitors (for example, attending physicians at a hospital) who are not your employees but still should be given special access. Maybe their devices get registered for a month at a time with no need for a password in between. Their WiFi may even have more bandwidth, i.e. perform better, than true guest WiFi does.
- “I think people are impressed when I have an elaborate system where I text them a one-time code which they enter to access the guest WiFi for 24 hours. I think it proves they accepted the terms and conditions. I think they think I have great security when I do that.” Maybe that’s how you feel, but maybe ask some of your guests before you jump to this elaborate conclusion.
- “What if I don’t want to provide guest WiFi at all?” But if you take this position, consider how you feel when you show up somewhere and the guest WiFi is awful or non-existent. Do you get any kind of warm and fuzzy for the folks you’re visiting? Sure there are certainly security concerns and physical spaces where you cannot allow access to the internet that is not strictly controlled. But guests to a facility like that are more than likely to understand those kinds of constraints.
The bottom line here is that guest WiFi is one of those areas where the security professional should be sure they are not over-securing the environment. And, on a related note, if you haven’t changed the default password on the admin account for your wireless access point at your house, now’s the time. Get going.